Introduction
At Roadie, we think deeply about the security of every feature we roll out. This has sometimes slowed us down, or meant that we've had to run without some features or plugins available. For example, we've written at length about steps we take to properly authenticate access for GitHub Apps.
Last year, to ensure our customers security, we made the hard decision to launch Roadie Backstage with the scaffolder disabled. This cost us some customers over the past 6 months, but it was worth it for security.
Today, after months of hard work, we are proud to launch scaffolder support with a completely re-designed and hardened architecture. This new architecture ensures that scaffolder tasks are run in an isolated and ephemeral environment which keeps customer data secure.
The scaffolder is available on all Roadie Backstage environments today.
To use it, start a free trial here, then check out our docs for the scaffolder, and read our walkthrough to learn how to write scaffolder templates.
What is the scaffolder?
Imagine you're an engineer looking to create a new microservice. You want to get started as quickly as possible, with minimal boilerplate and red-tape to jump through. At the same time, engineering organizations benefit from having consistency in production, and often put gates in place to enforce it.
Instead of creating blockers for engineering teams, Spotify use the scaffolder and quickly create new microservices, while helping to ensure that production remains mostly consistent.
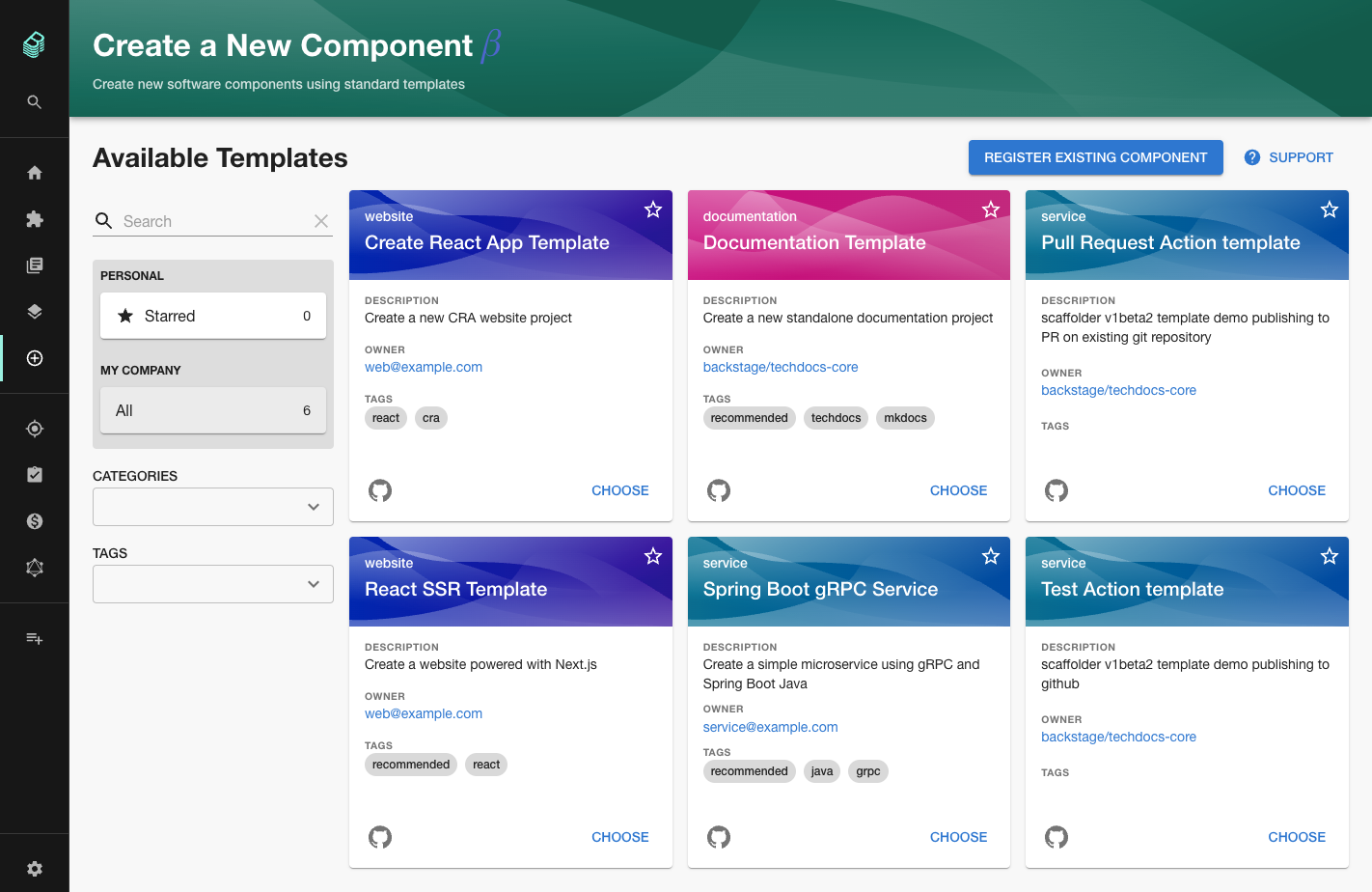
Engineers can choose a pre-defined software template, fill out a few form fields to provide values like the name of the GitHub repo that the new service will occupy, and click a button to run the template and create a the new service.
By making it easier to start new projects, your engineers can move more quicly, while preserving standaeds and reducing complexity in your tech ecosystem.
See it in action in this 3 minute video where we demo a scaffolder template which creates a GitHub pages website.
Roadie's scaffolder architecture
Before starting the work to enable the scaffolder, we audited the open source scaffolder actions one by one and found that the Backstage Scaffolder was running them on the API backend process of Backstage. Scaffolder tasks technically had access to the same resources available to the API backend.
Tasks that copied files or accessed network resources might are a little risky even when running Backstage inside your corporate firewall. On a SaaS platform like Roadie, they are unacceptable.
To isolate our scaffolder jobs, we run them in a separate process in a private network on AWS ECS. A single container task is spun up for each execution and destroyed once it completes.
The container can only access to its own Backstage database and the public internet. The container does not have access to the network services available to the API backend process and it cannot do things like copy files from the local API backend services file system.
We already support the most frequently used scaffolder actions on Roadie. You can fetch pre-defined templates, use them to create GitHub repositories and write to the Backstage catalog.
You can even send HTTP requests to the public internet, using an open source library we created, so that newly templated microservices can automatically register with your SaaS tools like Circle CI or PagerDuty.
The full list of supported scaffolder actions is available inside your Roadie Backstage instance at https://[sub-domain].roadie.so/create/actions.
Next steps
We're going to continue working on the scaffolder to make it faster, more featured and more secure. We're already thinking about features such as custom container support and fully custom scaffolder actions.
We've also begun publishing more open-source modules for the scaffolder . We've already created a general utils package and some dedicated AWS actions.
If there's something you'd like to see, please reach out on our public Discord channel .
